Baffled by Incidents? Security incident handling made easy.

STORM supports your team in delivering efficient incident management.
Time savings through proven security processes
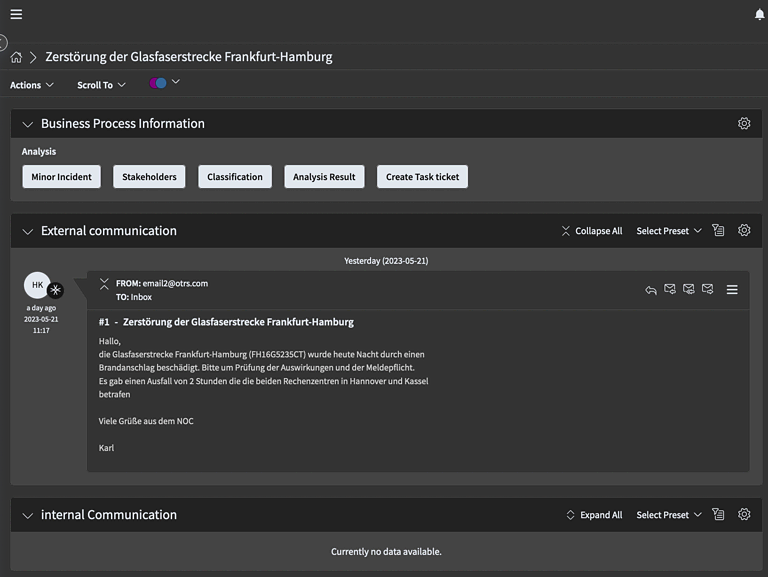
Faster and accurate handling of process steps through predefined and proven security processes that are aligned with leading taxonomies and frameworks. Communicate with the right people and connect the right tools – get all hands on deck fast. STORM communicates with third-party tools using integrated web services.
Security and compliance are a top priority
STORM supports digital encryption and signing standards, like PGP and S/MIME. Our solution is audit-ready. The documentation of all activities, such as the artifacts and the forensic evidence analysis, are tracked and can be audited at any time. STORM can be used in a completely offline environment.
Get started right away
Our experts have everything preconfigured for you. STORM comes with pre-defined classifications and ready-to-use incident processes. There's no time-consuming configuration or setup required. You can simply start right away and forward all support requests via email to STORM.
Award-winning quality
STORM was developed on the foundation of OTRS Service Management Software into a full-fledged Incident Response System including SOAR functionalities by the security experts of OTRS Group.
Get started with STORM today. Choose response over risk now.
In addition, STORM has already won awards, including the Incident Management Infosec Award in the “Cutting Edge” category.

Typical use cases
STORM is not just a cyber defense solution. It is also the solution for corporate security and the defense and security sector in general. It is suitable for ITSM use cases that have increased security requirements as well as for high-security applications in the military, BOS or defense industry.





Functionalities
Benefit from professional STORM features that relieve your security team, make work faster, reduce errors and support evaluation.
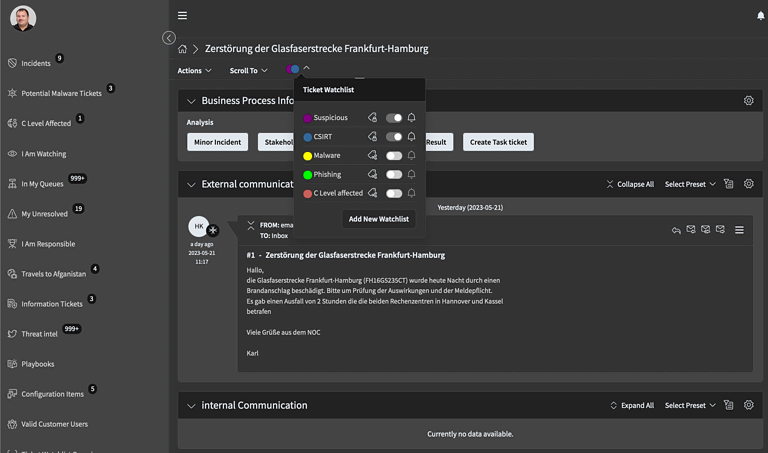
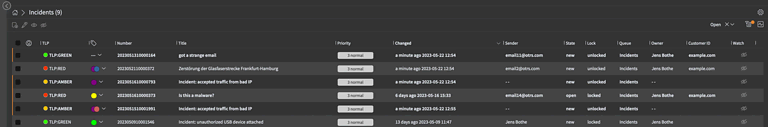
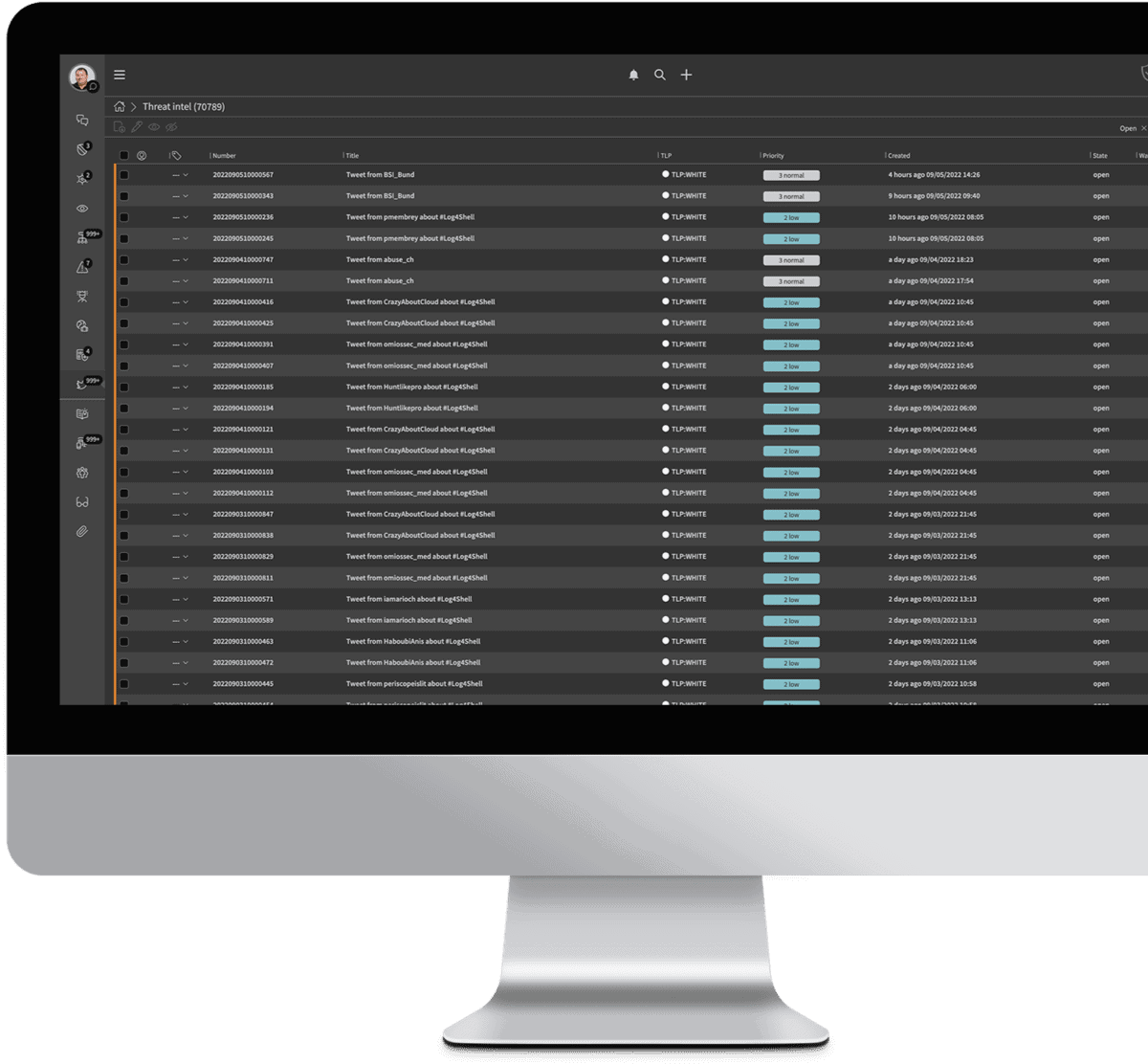
Easy Tagging of Incidents, Events, Cases and Attachments
Events, incidents, assets and other tickets can be easily tagged. The tags can be used as filters in the list views. Define labels individually and/or across teams for more structure in daily work. This gives you a better overview of already existing information and classifies your analysis results.
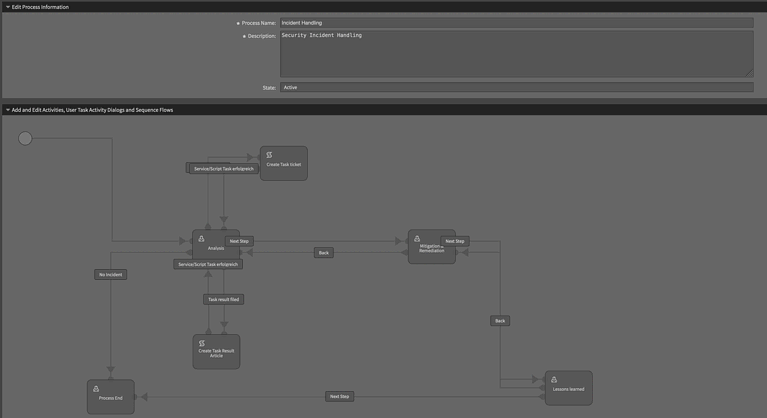
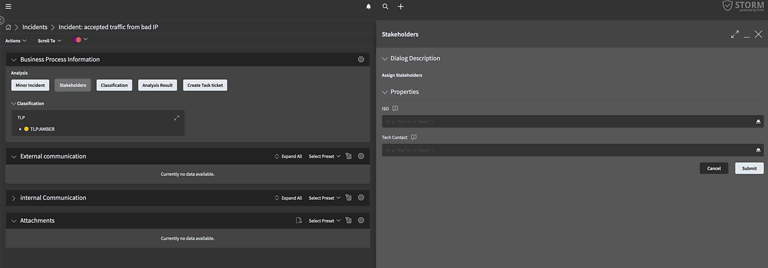
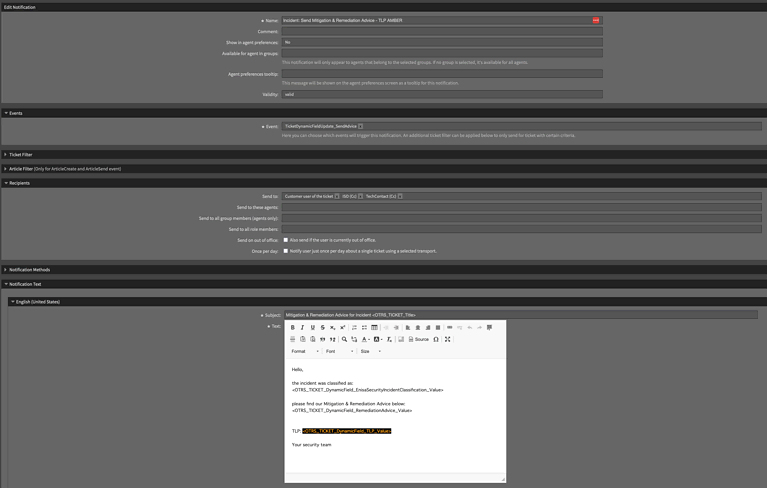
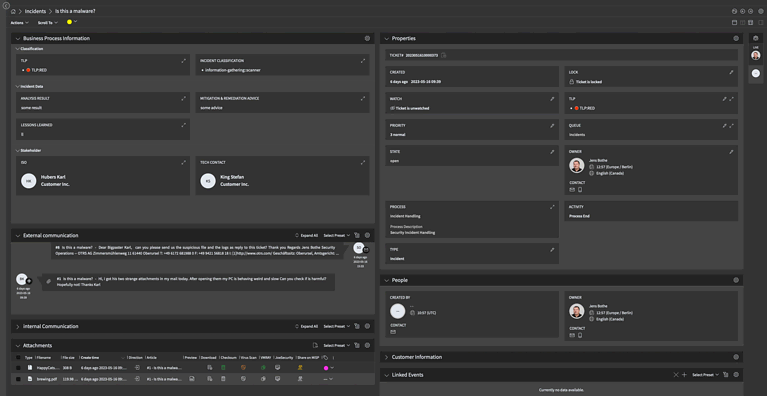
Automation and Processes
STORM offers the possibility to map processes and workflows as well as to automate them where necessary. A variety of field types help to capture data in a structured way and make it possible to evaluate activities. With the help of templates, new processes can be adapted quickly. Rule-based stakeholders and role-related notifications can be conveniently mapped.
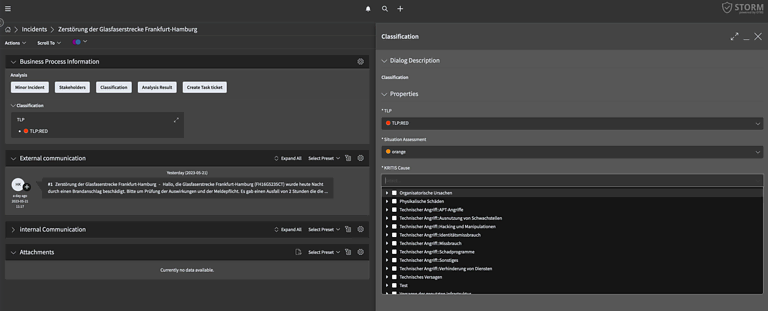
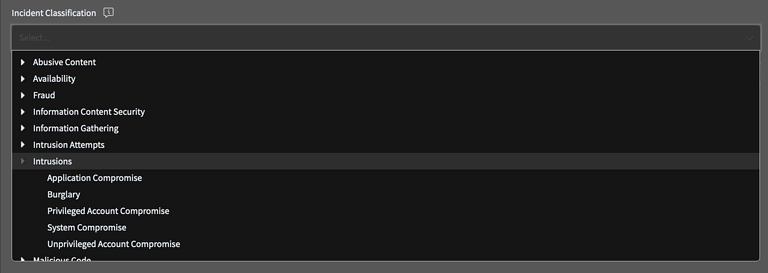
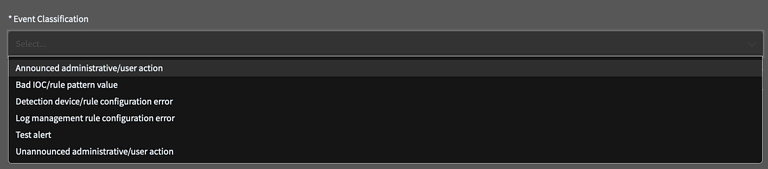
Predefined Taxonomy Fields for Easy Reporting and Classification
Predefined classifications for incidents and events allow for simple taxonomy-based classification according to established standards. These include KRITIS-compliant classification (according to §8b paragraph 4 BSIG) as well as ENISA‘s Reference Security Incident Classification Taxonomy.
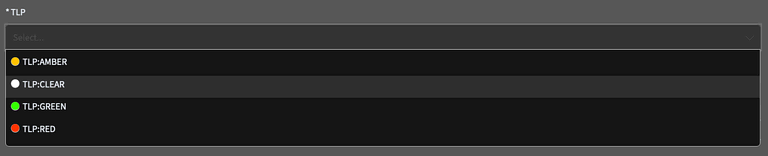
STORM also offers the possibility to classify information using the Traffic Light Protocol (TLP) and to use this classification in notifications.
Additional classifications can be easily added.
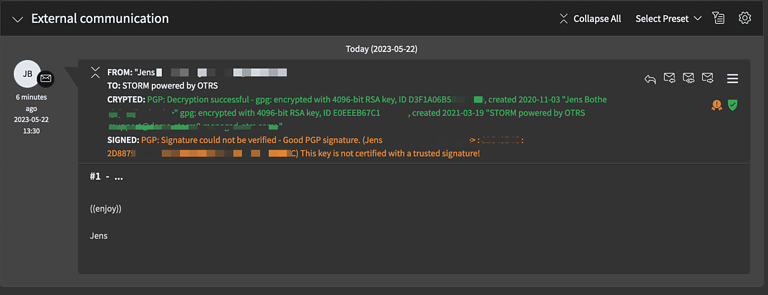
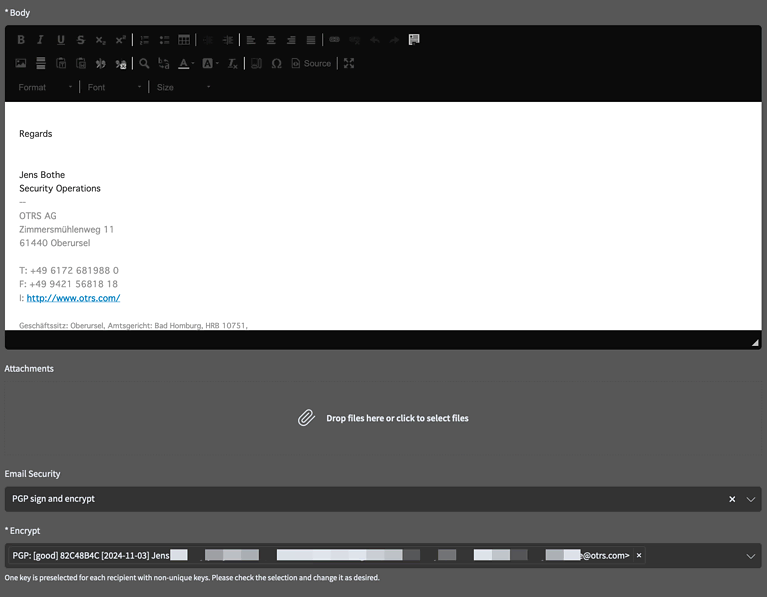
Enhanced Encryption Features via PGP & S/MIME (HSM supported)
Benefit from the advantages of end-to-end encryption and signing communication via PGP & S/MIME. Private keys on hardware security modules can also be used for encryption and signing.
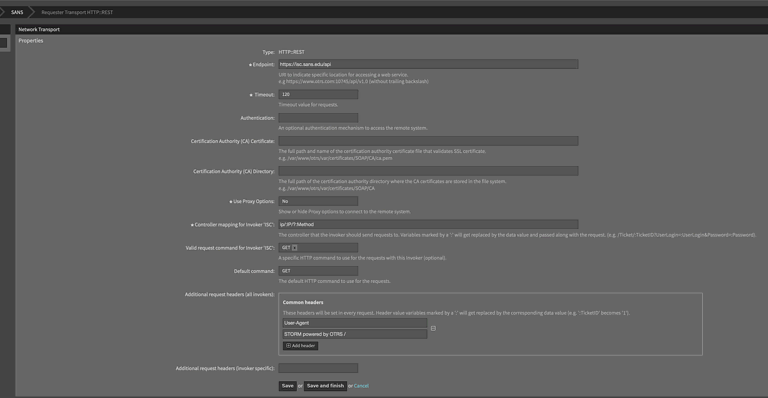
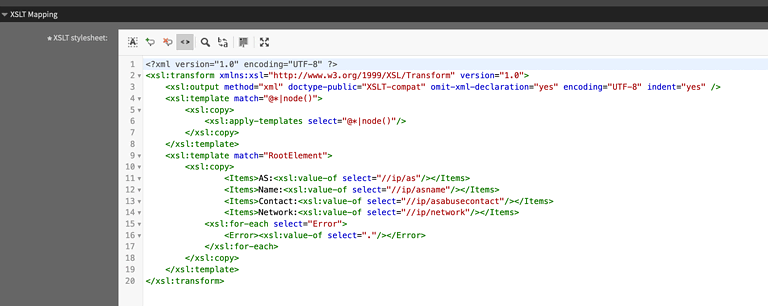
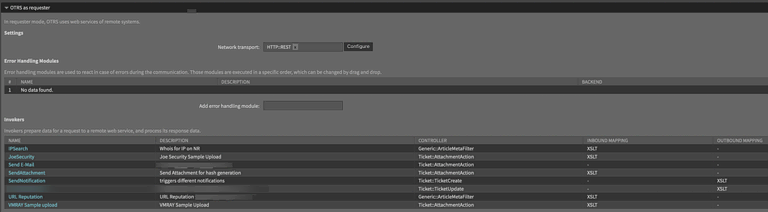
Integration via Web Services
STORM has multiple possibilities to interact with third party applications via open web service standards. Data can be sent to other tools automatically or based on a process workflow, and the responses can be processed in the system. Events, incidents and other requests can also be opened via this path.
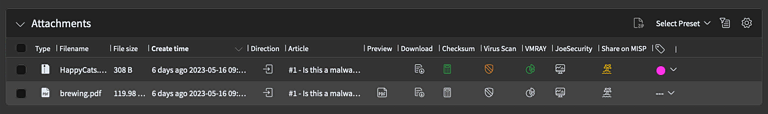
Predefined interfaces to VirusTotal, VMRAY and other solutions allow fast adaptation to existing workflows.
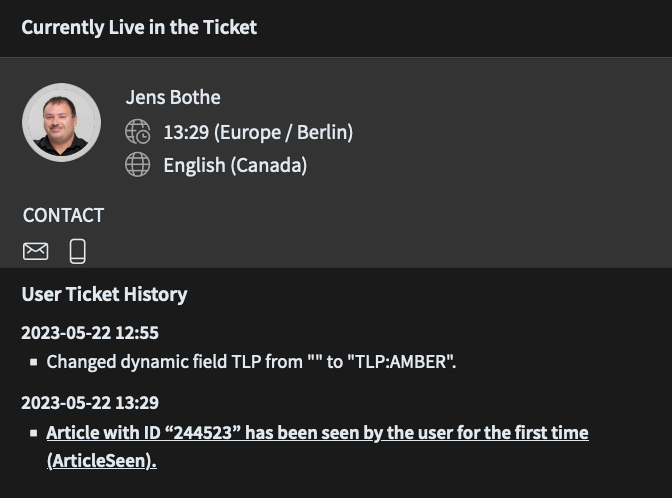
Compliance Logging Features
All ticket actions are logged. This makes it possible at any time to track who has added, changed or read which information. The download of attachments is also logged.
STORM Solution Service Packages
GREEN
On-Premise
-
9:00 am - 5:00 pm weekday support
-
10 Concurrent Agent Sessions
-
Web Services
AMBER
On-Premise
-
8:00 am - 8:00 pm weekday support
-
25 Concurrent Agent Sessions
-
Web Services
-
Air Gap System (optional)
RED
On-Premise
-
24/7/365 support
-
100 Concurrent Agent Sessions
-
Web Services
-
Air Gap System (optional)
