

What is ISO/IEC 27001?
ISO/IEC 27001 is an international standard that defines how organizations should operate and maintain an information security management system to best address emerging information security risks.
ISO/IEC 27001 further describes the requirements for assessing and addressing the information risks that apply to a particular company or organization.
Why is ISO 27001 certification important?
Certification of an ISMS according to ISO/IEC 27001 standards is an important statement on the quality of a company’s ISMS and its risk management practices.
Additionally, certification is a prerequisite for many investors and partners who see this as a signal that they can securely cooperate with a business. In many parts of the world, it is even legally mandatory.
The certification helps businesses set up and operate an ISMS in a structured manner and in accordance with international standards that are specified by a series of controls.
Becoming certified has the following benefits for a company:
- Identifies risks
- Reduces liability risks
- Protects data
- Provides peace of mind for employees
- Increases trust in the company and its Governance, Risk & Compliance Management (GRC), and
- Increases competitiveness
If you know all the risks, the risks don't get smaller, but the risk of falling victim to them goes down.Georg Wilhelm Exler
Who needs ISO 27001 certification?
Any company can benefit from pursuing ISO 27001 because of the many risk avoidance and trust-building benefits that it offers.
However, some businesses are required by law to obtain formal certification. For instance, in Germany, all businesses that are identified as critical infrastructure (German: KRITIS ) must complete certification. In the United States, there are not any laws that bind companies of any industry to ISO 27001. It is important to investigate your local laws to determine if your business is legally required to obtain ISO/IEC 27001 certification.
ISO 27001 Compliance vs. ISO 27001 Certification
Any company that takes steps towards implementing ISO 27001 is professionalizing its approach to information security and risk management; however, this does not mean that they will all get the benefits of ISO certification.
ISO 27001 compliance means that a company has evaluated itself in terms of meeting all of the criteria set forth by ISO 27001.
ISO 27001 certification, however, is more powerful. It means that a third-party certification body has audited the implementation and management of the ISMS and related controls at a company. More trust is built because someone outside of the company is making the claim of completeness on the company’s behalf.
What are the requirements for ISO 27001 ISMS certification?
Basically, the requirement is that a company maps all security-relevant topics, responsibilities, information, emergency plans, and processes in the ISMS and clearly defines responsibilities for overseeing these.
The maintenance and updating of the ISMS are also mandatory to ensure that a company responds to changes in the company and associated risk landscape.
Before embarking on certification, companies must have the following in place.
Organization
- The organizational chart of the company
- Definition of responsibilities & stakeholders
- Justification for the application (Statement of Applicability)
- Analysis of the ISMS classification within the company
- Analysis and definition of the respective stakeholder requirements
- Overview of all legal and regulatory requirements for information security in the company and their impact on the ISMS
Leadership
- Documentation of information security goals and requirements
- Definition of the information security strategy
- Definition of ISMS management and the required resources
- Implementation of an information security policy
Planning
- Documented risk assessment process
- Detailed documentation of the risk mitigation process
- Results of risk assessments and analyses
- Risk mitigation results
- Definition of information security goals and objectives for all stakeholders
Support
- Communication plan, covering internal and external communication, regarding information security topics
- Infrastructure and available people to implement and operate the ISMS
- Strategy for handling the documented information
- Overview of budget and necessary resources
- Detailed description of all roles with proof of competencies
- Documented training concept for the ISMS
- Training documentation and evidence of employee training
Operation
- Evidence of the performance and correct execution of the ISMS processes
- Documented audit programs and their results
- Existing incident response plan, including contact lists and escalation plans
- Documentation of KPIs and their collection processes
- Rules of conduct, processes, and their description
- Work instruction for evidence collection in case of information security incidents
- Evidence for handling and managing information security deviations
- Results of risk assessment and risk mitigation
The ISO 27001 certification process
The certification process is divided into eight phases. Sufficient time should therefore be planned for preparation and implementation.
-
Preparation
Checking for completeness of the documents and items described above as well as the documentation of the ISMS and compliance with the specified standards. If necessary, the auditor should already be involved here as they may be able to offer suggestions and recommendations to help the company.
-
Audit
The audit includes the review of all documents, certificates, and processes of the ISMS with subsequent examination of their effectiveness. It may also involve speaking directly with employees about their understanding of and impact on the ISMS.
-
Assessment and report
The auditor prepares an evaluation of the results from the audit and final report.
-
Planning
In phase 4, the activities resulting from the audit are planned.
-
Implementation
Subsequently, the measures resulting from the audit are implemented and documented.
-
Certification
In the 6th phase, the certification of the ISMS is carried out with a maximum duration of 3 years.
-
Annual Audit
After receipt, an annual internal review of all information security measures taken in the ISMS must take place and be documented.
-
Extension of the certificate after 3 years
For the extension, the 7 previous phases are simply repeated.
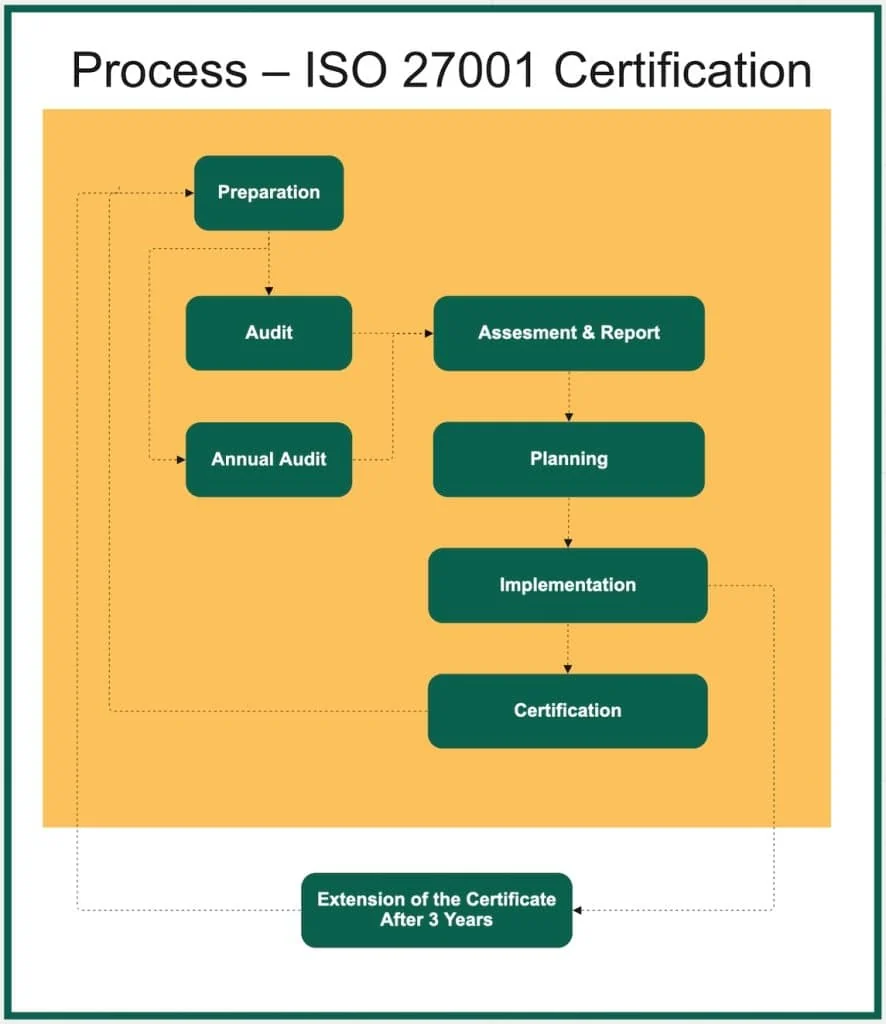
Process-ISO 27001 Certification
The cost of ISO 27001 certification
It is difficult to give a general estimate of the costs of certification. Basically, it depends on the size of the company as well as how long it will take to review all of the security-relevant information and processes that have to be mapped in the ISMS.
The cost range for an ISO 27001 certification, from 6,000 to 30,000 USD. And, of course, the cost of any activities that are identified during the assessment and report phase must be considered as well.
Follow-up costs
For the following audits in the two years after certification, further costs arise that should be clarified. The certificate renewal, which is necessary after the third year, must also be considered in the budget planning.
ISMS Software according to ISO/IEC 27001
Often, you still find an ISMS cumbersome to manage, because they consist of a summary of different documents or a variety of different sources.
Central maintenance is often not possible. Adequate information security management and necessary audits can only be guaranteed with great effort.
The right software means avoiding risks and saving money
With the right software, however, companies can document all assets, evidence, and responsibilities. They can track the status of controls and quickly prepare for audits. ISMS processes help to implement the PDCA (Plan-Do-Check-Act) cycle. And access management and audit security of modern ISMS software offer further significant advantages in the operation of an ISMS.
Learn how to implement ISMS processes easily from our experts.
Categories
- About OTRS Group (21)
- Automation (3)
- Corporate Security (26)
- Customer Service (30)
- Developing a Corporate Culture (12)
- Digital Transformation (54)
- General (86)
- ITSM (36)
- Leadership (22)
- OTRS in Action (8)
- Processes (5)
- Using OTRS (15)
