

More explosive than ever, the challenge facing corporate teams is protecting sensitive information and data, as well as IT systems, from increasingly frequent cyber attacks. In large part, this is because of the high costs caused by possible attacks.
Therefore, cyber security tools are a must for cyber security and data protection of the company and its employees. The goal of cyber security tools: to protect the IT network, IT systems and all applications from possible cyber attacks. Unauthorized data access, cyber attacks and identity theft should be avoided as much as possible.
How important is cyber security?
With the increasing interconnectedness of the world – Industry 4.0, Internet of Things (IoT), new digital working worlds – we enjoy many times more freedom. But at the same time, the risk of attacks, cyber attacks, is also increasing. The topic of cyber security is still treated as a secondary concern in some companies.
But what good is a highly digitalized production process if it is easy for a hacker to intercept sensitive data via a coffee machine connected to the Internet? What use is a smart home for spending time on the finer things in life if the occupants have to reckon with being hacked at any time?
To companies, the contradiction is obvious: What are the benefits of extensive networking if, and when, downtime cannot be minimized or even eliminated after a successful cyber attack?
The best protection against cyber attacks is using cyber security tools. We will now shed light on what types of tools are available.
Cyber Security Tool Categories
The following types of cyber security tools can be defined:
- Network Security Monitoring Tools
Network security tools monitor network traffic. When known and/or unknown security threats are detected, they send alerts to the IT security team. They can perform various investigations to protect data, contain the damage and resume normal operations. - SOAR Software
In conjunction with a SIEM tool, SOAR software reacts when a potential security threat is detected. Using predefined processes, the appropriate security team is informed about the information. It orchestrates varous secuirity tools, and it offers many possibilities to optimize processes and workflows. - Encryption Tools
These tools encrypt data and disks from unauthorized access. - Web Vulnerability Scanning Tool
A vulnerability scanning tool scans IT systems and their networks for vulnerabilities, identifying possible security holes. - Packet Sniffer
These monitor data within a network and are part of security monitoring. In doing so, they examine flowing data packets that move within a network or the global Internet. - Antivirus software
Malware is found and removed by these programs. In some cases, they also prevent attacks and the infection by such malware. However, this requires that the malware is already known or suspicious behavior is detected. Quarantine mechanisms are also frequently used here. - Firewall
A firewall is an IT system that analyzes, forwards or, if necessary, blocks data traffic. Firewalls come in various forms, from simple port filters to systems that also analyze the content of packets. - PKI
PKI stands for “Public Key Infrastructure.” Digital certificates can be issued, distributed and verified which ensure secure and encrypted exchange of data on the Internet. - Managed Detection Services
A managed detection system offers threat intelligence, threat hunting and analysis all in one tool.
Below we would like to introduce you to some cyber security tools.
When it comes to your sensitive data and protecting your system, only the combination of multiple tools, procedures, mindset and awareness ensures security.
Comparison of Cyber Security Tools
The HiveProject
The HiveProject is an open source security incident response tool – tightly integrated with MISP (Malware Information Sharing Platform). SOC and CERT analysts can see all information in real time. Events or incidents reported by MISP can be immediately imported and investigated.
Phantom
The tool “Phantom” is SOAR software from SPLUNK. It helps automate repetitive tasks and can be linked to other systems.
IBM Resilient
IBM Resilient captures and codifies incident response processes into playbooks to provide a security team with knowledge to remediate incidents. It can also visualize security incidents to prioritize and take action.
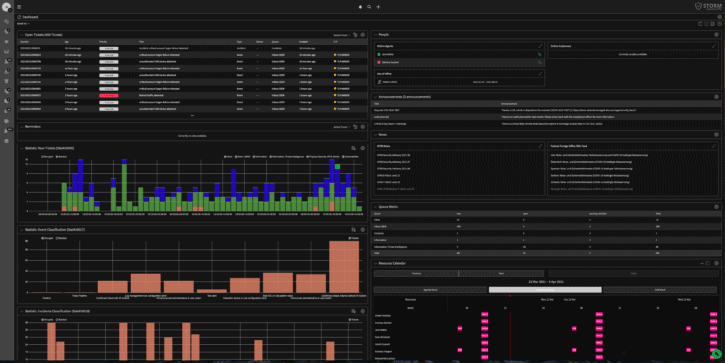
STORM powered by OTRS
STORM SOAR software prioritizes, categorizes and automates security incidents. Orchestration, automation and response to these incidents are managed instantly. The big plus of this tool: Digital encryption, signing standards (PGP and S/MIME) and auditability of communications for all events/incidents. Plus, there is no lost time due to predefined processes defined in the tool for security teams.
STORM SOAR Software bedeutet top Incident Management.
Orchestrierung | Automatisierung | Reaktion | Kommunikation
Mehr über STORM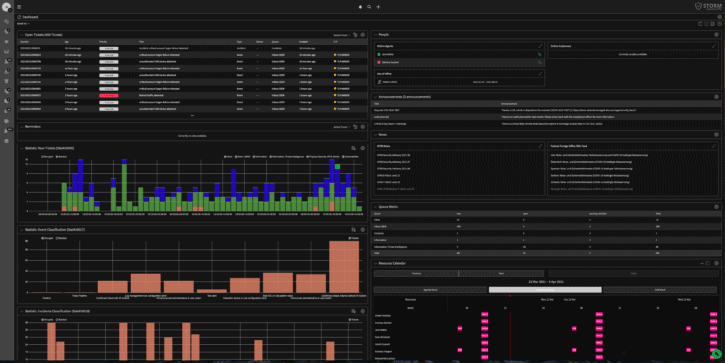
STORM SOAR software means better incident management.
Orchestration | Automation | Response | Communication
More about STORMCategories
- About OTRS Group (21)
- Automation (3)
- Corporate Security (26)
- Customer Service (30)
- Developing a Corporate Culture (12)
- Digital Transformation (54)
- General (86)
- ITSM (36)
- Leadership (22)
- OTRS in Action (8)
- Processes (5)
- Using OTRS (15)
