

What is an Incident Response Plan?
An Incident Response Plan (IR Plan) is a predefined process and is part of incident management. It is established by companies to respond to security incidents. It is a prerequisite for effective and efficient incident response measures. It includes guidelines, procedures and activities that are used to recognize, evaluate and combat threats. An IR plan also helps restore normal operations after an incident.
The plan typically includes roles and responsibilities, escalation paths, communication protocols and technical steps to deal with security incidents. By implementing such an IR plan, organizations can respond efficiently to threats to minimize potential damage and protect business operations.
Who needs an Incident Response Plan?
An incident response plan is typically expected by organizations that:
- process sensitive data,
- operate critical infrastructure (KRITIS) or
- provide services to other organizations where the availability, integrity and confidentiality of data is critical.
This includes companies in many industries such as financial services, healthcare, government agencies and telecommunications.
An incident response plan is required to enable organizations to respond appropriately to security incidents. It helps minimize the impact of incidents, maintain operations and preserve customer and stakeholder confidence. In addition, certain industry regulations or legal requirements may mandate the development and implementation of an incident response plan.
What information must be included in an incident response plan?
A formal incident response plan is essential for organizations to respond appropriately to security incidents. Below is a list of the key information that should be included when you create an incident response plan:
- Contact information for the Incident Response Team and other relevant stakeholders
- Procedures for reporting security incidents
- Definitions of the different types of security incidents and their severity levels
- Assignment of roles and responsibilities for the incident response team
- Escalation paths for serious incidents or unexpected challenges
- Instructions for detecting, analyzing and containing security incidents
- Communication protocols for internal and external stakeholders, such as law enforcement or customers, during an incident
- Technical instructions for restoring normal operations and preserving evidence
- Procedures for reporting, documenting and evaluating security incidents
- Update and review processes to ensure the plan remains current and effective
How is the Security Incident Response Plan adapted to Individual Company Requirements?
To ensure a tailored response to security incidents, the incident response plan must be adapted to the conditions and requirements individual companies. This makes it an effective tool – and meets the specific needs and challenges of each company.
The following aspects should be taken into account:
Risk Assessment
Risk assessment enables companies to make informed decisions about the allocation of resources and the prioritization of activities for protecting against security incidents. It ensures that the IR Plan adequately addresses current threats.
Risk assessment in the Incident Response Plan includes the identification, evaluation and prioritization of potential security risks. It evaluates the source of the threats, the probability of their occurrence and the potential impact of incidents on the company. Additionally, the identification of critical assets and the analysis of existing security measures help with the risk assessment.
Risk mitigation measures are prioritized and integrated into the incident response plan based on the results of the risk assessment..
Risk Assessment Methods
Various assessment methods are used. These include qualitative and quantitative analyses, risk matrices and scenario analyses.
The selection of the appropriate risk assessment method depends on various factors, including:
- the type of company,
- the available resources and
- the specific security requirements.
A combination of several methods is often used to obtain a comprehensive picture of the risk landscape. Qualitative methods are one. An example of this is the use of a risk matrix and threshold analyses. This assess risks based on their probability of occurrence and impact.

Quantitative methods use numerical data and models to quantify risks. Examples of this can include cost-benefit analyses or probability calculations.
Scenario analyses describe various security incidents and assess their potential impact.
The choice of method depends on the specific requirements of the company and available resources.
Stakeholder Involvement
Stakeholders are people who may be affected by an incident. It includes internal and external people. Clear communication channels must be established with stakeholders. They must be regularly informed about incident response activities. Stakeholders are also actively involved in the plan through training and regular exercises.
Resource Allocation
Resource allocation means that personnel, technology and budget are allocated according to the severity and urgency of the security incident. Companies should use resources efficiently to ensure that incidents and security breaches are dealt with effectively.
Compliance Requirements
Compliance with relevant laws, regulations and industry standards is defined. This may include data protection laws, reporting obligations for security incidents and industry-specific compliance requirements. The plan must define policies and procedures that meet all legal requirements.
The plan also outlines incident response steps for communicating with regulatory authorities, other external partners and customers in the event of a security incident.
Corporate Culture
In addition to the Incident Response Team, the integration of the Incident Response Plan into the existing corporate culture should be considered. It is important that implementation be as smooth as possible.
The Incident Response Plan Template
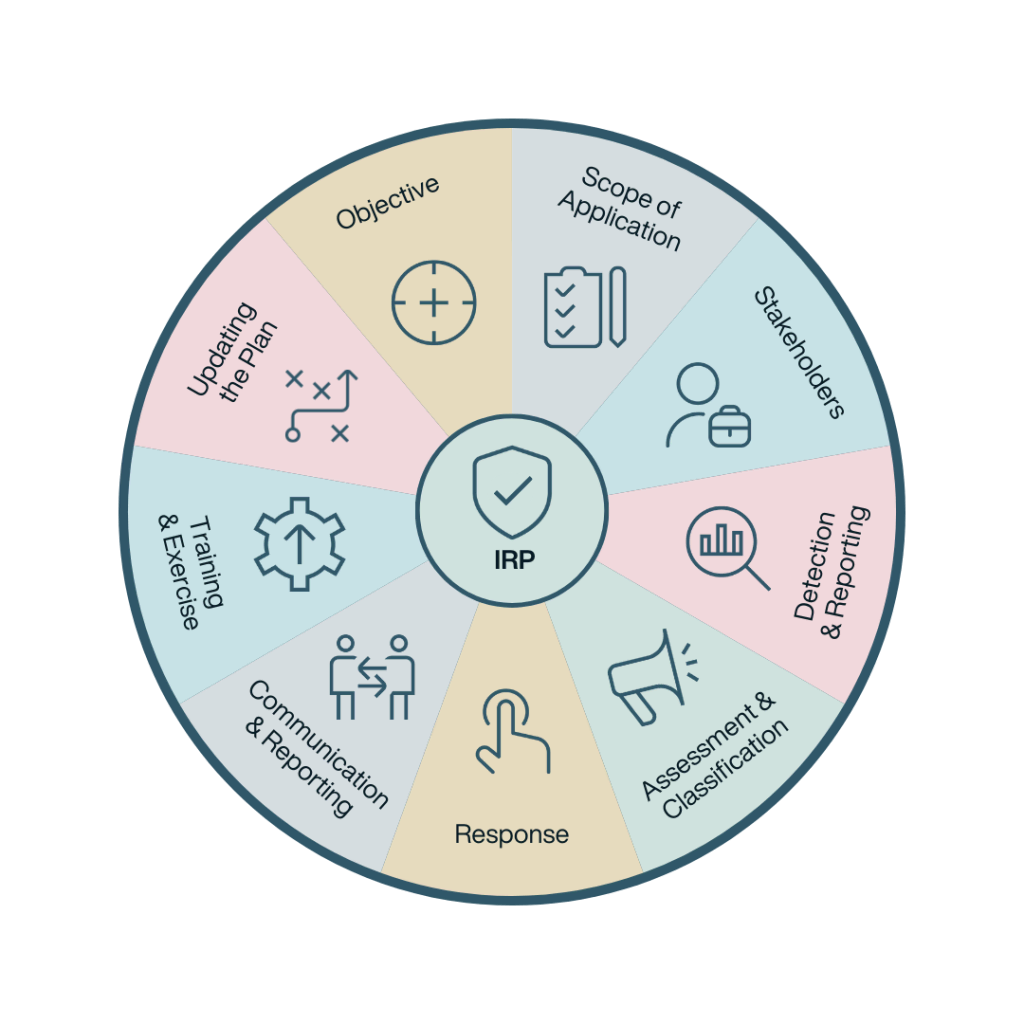
Scope of the Incident Response Plan
An incident response plan template should provide clear structure for each area of incident response. The template can be adapted to the needs of the company. It covers all phases of incident response and outlines the response process(es).
The following topics belong to an individual plan:
Purpose and Objective
- Describe the importance of an Incident Response Plan.
- Explain its purpose and when it is to be used.
- Clearly formulate the plan’s objectives, such as minimizing downtime and limiting damage.
- Explain how the plan helps to secure the company and meet compliance requirements.
Scope
- Define the areas of the company to which the plan applies.
- Clearly outline types of incidents covered by the plan.
Incident Response Team
- List the incident response team members with their respective roles and responsibilities.
- Include team member contact details for faster communication during an incident.
Incident Detection and Reporting
- Identify possible incident types.
- Describe the various methods and security tools used for detection.
- Define procedures for reporting incidents to the incident response team, including escalation paths.
Incident Assessment and Classification
- Explain the criteria for assessing the severity and urgency of security incidents.
- Define the system for classifying various incident types.
Incident Response Process
- Describe incident handling and serve to contain security incidents. Immediate measures must also be defined here.
- Describe investigation steps for determining the causes and effects of incidents.
- Write instructions for restoring systems and data after an incident in order to restore normal operations.
Communication and Reporting
- Define internal and external communication protocols for use during an incident.
- Specify documentation and reporting requirements that are needed for internal and external purposes.
Training and Practice
- Define training programs for employees. These will raise awareness of potential threats and security incidents within the company.
- Plan and conduct regular exercises and simulations to improve the team’s ability to respond.
Updating and reviewing the plan
- Lessons learned: Experience from the incidents should be incorporated into the plan in order to react better to future incidents.
- Establish procedures for regularly updating and reviewing the plan. It must correspond to the current threats and requirements of the company. Review and updating keep the plan relevant long-term.
- Define responsibilities for updating and reviewing the plan.
Incident Response Roles and Responsibilities
The following roles and their respective tasks should be considered in the incident response plan. These may vary depending on the specific requirements and size of the company. They represent the basic structure for creating an effective incident response team.
Incident Response Team Leader
- Coordinates the entire incident response team during an incident
- Monitors and manages the response to the incident
- Communicates with senior management and other relevant stakeholders
Incident Analyst
- Analyzes security incidents to understand their causes and effects
- Assesses the severity and urgency of incidents
- Collects evidence and relevant data to support further investigation
Network Security Specialist
- Monitors and analyzes network traffic to detect potential attacks
- Implements network security measures and incident containment
- Supports network restoration after an incident
System Administrator
- Monitors and manages the company’s systems to identify potential vulnerabilities
- Implements security patches and updates to minimize risks
- Supports the recovery of systems after an incident
Legal Advisor
- Advises the incident response team on related legal issues
- Supports compliance with laws, regulations and data protection provisions
- Assesses legal risks and the potential impact of incidents
Public Relations Representative
- Communicates with the media and the public during a security incident
- Provides information and updates about the incident to maintain customer and public confidence
- Protects the company’s image and reputation during and after an incident
Human Resources Coordinator
- Coordinates employee awareness and training activities related to security incidents.
- Supports the communication of incident reporting policies and procedures
- Supports employees affected by an incident
Incident Management According to ITIL®
ITIL Incident Management is part of the IT Infrastructure Library (ITIL) framework. The framework provides best practices for IT Service Management (ITSM).
The goal of ITIL Incident Management is to minimize the impact of security incidents on IT operations and to ensure service continuity. The following steps are typically listed in the ITIL Incident Response Plan:
- Incident recording
- Incident classification
- Incident prioritization
- Incident investigation
- Incident resolution
- Incident documentation
- Incident escalation
- Incident closure
Simplifying Incident Response Activities
The IR plan is the first step all companies must take. It provides guidance for companies during a critical time.
Clearly, handling incidents is complex and requires on-going dedication. Many companies, therefore, operate specially trained cyber security incident response teams (CSIRT – Cyber Security Incident Response Team) to respond appropriately to potential incidents.
Companies also use software to help speed up response. A software solution that automates incident management processes keeps everyone on track. Workflows are clearly defined for the incident response management team. Steps required for documentation, communication and more are automated so that they move swiftly and nothing is forgotten. This provides a secure and effective framework for incident management.
With the OTRS ITSM solution, you benefit from a preconfigured incident management process according to ITIL 4. It can even be customized to your individual business requirements – as outlined in your incident response plan.
Categories
- About OTRS Group (21)
- Automation (3)
- Corporate Security (26)
- Customer Service (30)
- Developing a Corporate Culture (12)
- Digital Transformation (54)
- General (86)
- ITSM (36)
- Leadership (22)
- OTRS in Action (8)
- Processes (5)
- Using OTRS (15)
